Secure. Verified. Monetizable.
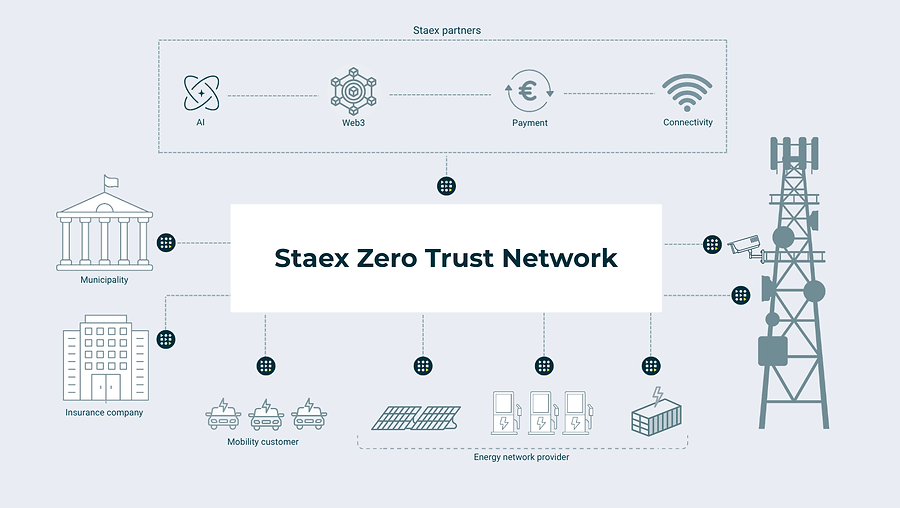
Staex is the verified-trust network layer that sits on top of the AWS, SAP and SaaS systems your business already runs — turning them into a working, secure, monetizable agentic suite. No cloud lock-in, no integration project.
At its core, Staex replaces brittle networking with encrypted, peer-to-peer tunnels between nodes — each representing a device, service, or system in your business. Every connection gets its own keys and protocol, so traffic stays isolated and verifiable end to end.
Reimagine What Your Machines Can Do
Instantly Deploy Networks
Connect machines and services across locations, partners, and customers in minutes — not months. No VPN appliances, no firewall rules, no cloud dependencies.
Secure Every Connection
Verified trust and tunnel-based communication ensure privacy and control. Each connection gets its own keys and protocol — no lateral movement, no broadcast surface.
Monetize Device Data
Enable trusted data exchange and on-chain anchoring, letting you create revenue streams from machine telemetry and real-time analytics.
Automate Device Management
Manage complex infrastructures with zero-touch updates, remote orchestration, and policy-based control from a single interface.
Cut Network Maintenance Costs
By eliminating traditional VPNs, complex firewalls, and centralized clouds, Staex dramatically lowers operational costs (up to 45%) while increasing uptime.
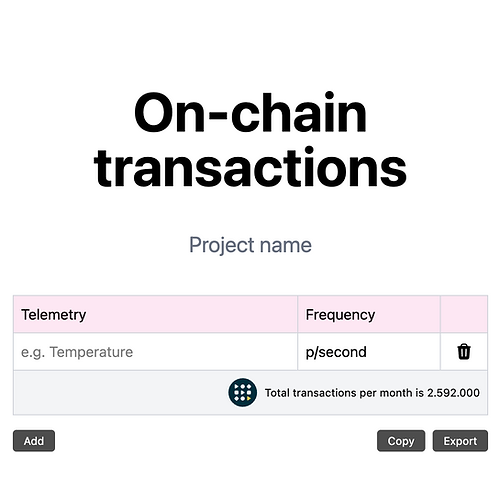
Staex TX Calculator
Estimate Your Network. Plan Your Growth.
With the Staex Device On-Chain Transactions Calculator, you can easily estimate the number of nodes, tunnels, and transactions your project needs. Enter your estimates or goals — and let us show you how Staex can power your ecosystem.
No signup required.
Try the CalculatorReady to Turn Your Estimates Into Reality?
Book a demo with our team and see how Staex can bring your device network — and your data — on-chain, securely and efficiently.