New Feature: System Network Interfaces Integration
2022-12-29
The new version of Staex reduces workload for system administrators and simplifies application integration.

The new version of Staex reduces workload for system administrators and simplifies application integration.
Latest version of Staex directly integrates with system network interfaces. This means that system administrators no longer need to perform REST API calls to publish services and open ports for clients to run applications over Staex network. Instead they bind services to Staex network interface and point clients to the service's address, and everything else is handled by Staex!
The process of setting up network interfaces is documented in our new tutorial. In most cases this boils down to assigning a unique IPv4 address to each node.
System network interfaces makes it even more transparent for the application to run over Staex network. In addition, they enable us to tunnel protocols that contain IP addresses as part of the packets (e.g. SIP) and protocols that dynamically send data to certain nodes based on some internal logic (e.g. DDS, MQTT and other implementations of the publish-subscribe model).
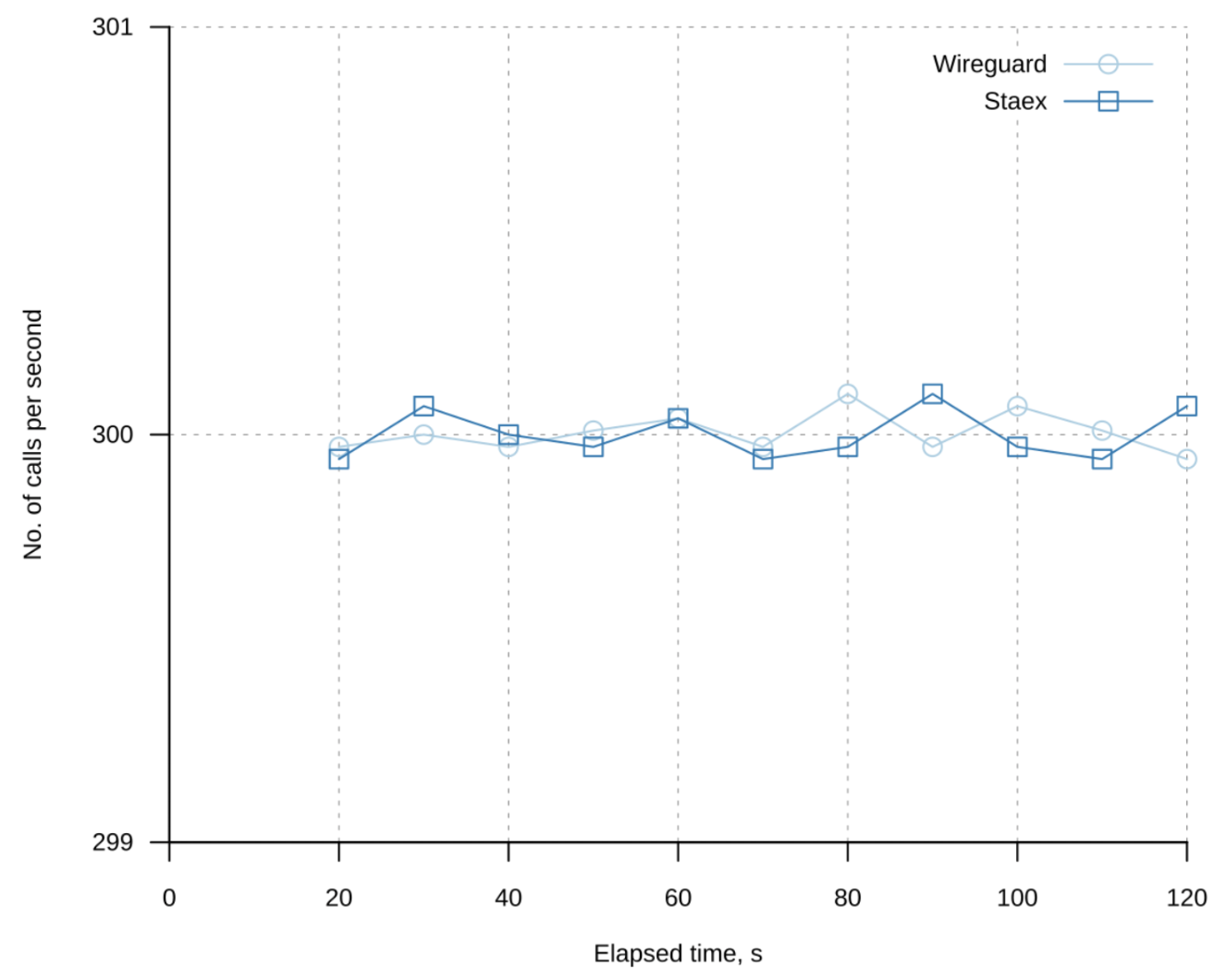
We benchmarked SIP protocol using SIPp tool and Kamailio SIP server. We found that Staex network shows comparable performance to Wireguard VPN in this case.
System network interfaces is an exciting new feature that opens up a lot of new possibilities that we haven't explored yet.


Staex is a secure public network for IoT devices that can not run a VPN such as smart meters, IP cameras, and EV chargers. Staex encrypts legacy protocols, reduces mobile data usage, and simplifies building networks with complex topologies through its unique multi-hop architecture. Staex is fully zero-trust meaning that no traffic is allowed unless specified by the device owner which makes it more secure than even some private networks. With this, Staex creates an additional separation layer to provide more security for IoT devices on the Internet, also protecting other Internet services from DDoS attacks that are usually executed on millions of IoT machines.
To stay up to date subscribe to our newsletter, follow us on LinkedIn and Twitter for updates and subscribe to our YouTube channel.

See also
Staex latest release features on-premise fleet management via web UI
2024-06-27
Web UI aims to streamline initial network configuration and fleet management without relying on cloud services.
Staex: Data Sharing for IoT
2024-06-17
In this article, we want to share how we achieved Web3 IoT data infrastructure utilizing Staex and PEAQ networks.
Geeny by Telefónica and Staex to build secure public network for remote machines and devices
2024-05-06
Geeny by Telefónica and Staex will provide building blocks for secure IoT connectivity in the field.


